 As technology continues to evolve, healthcare organizations of all sizes are working to remain current in what they can offer to providers and patients while also keeping PHI secure. Covered entities now have various options of communication, and HIPAA compliant email is often a necessity.
As technology continues to evolve, healthcare organizations of all sizes are working to remain current in what they can offer to providers and patients while also keeping PHI secure. Covered entities now have various options of communication, and HIPAA compliant email is often a necessity.
However, healthcare organizations cannot assume that any form of email communication will in fact keep PHI secure and adhere to HIPAA regulations. Even third parties are not always exempt from HIPAA compliance as they communicate with healthcare organizations.
As Linda McReynolds, Esq. & Ronald Quirk, Esq. explained in a HealthITSecurity.com contribution, it is important to understand the difference between companies that offer a “mere conduit” service and an actual business associate.
“Entities that provide ‘mere conduit’ service are excluded from HIPAA liability,” McReynolds wrote. “The mere conduit exemption applies to telecom or information services that exclusively provide transmission or temporary storage of transmitted data incident to such transmission. This includes entities such as internet service providers and paging carriers.”
Want to publish your own articles on DistilINFO Publications?
Send us an email, we will get in touch with you.
They key difference is the transient versus persistent nature of the opportunity to view the PHI.
“To qualify as a conduit, a service provider must ensure that PHI is only temporarily stored,” she explained. “It is irrelevant whether the service provider actually views the PHI.”
Healthcare organizations and business associates cannot assume that all forms of email are in fact HIPAA compliant email.
A study by Infinite Convergence Solutions, Inc. found that most healthcare organizations use secure messaging platforms that are not HIPAA compliant. However, the majority of respondents reported using email as their preferred channel of business communication, followed by mobile messaging and then voice calls.
When asked why they preferred email, those surveyed said they would rather compose an email or make a phone call, they do not like that mobile messaging leaves no paper trail, and that they do not think it is as secure as email or phone calls.
“Healthcare institutions need to get serious about meeting their employees’ needs and providing a secure, internal messaging platform that not only allows HIPAA compliance, but also replaces outdated communication systems, like pagers, in order to increase productivity and serve patients faster,” Infinite Convergence Solutions CEO Anurag Lal said in a statement.
With federal officials also working toward true interoperability, DirectTrust and its messaging options have taken on a larger role for secure email options.
DirectTrust is a non-profit trade alliance that facilitates secure HIE through the Direct Protocol and also forms secure HIE policies and standards. Furthermore, Direct also played a part in enabling the exchange of health information in federal healthcare initiatives such as the EHR Incentive Programs and Stage 2 Meaningful Use.
However, a common perception is that Direct only focuses on secure email. Why exactly should providers consider implementing this as part of their larger HIPAA compliant messaging program? If a hospital wants to utilize secure BYOD options as well, is Direct messaging the right choice?
Understanding hipaa compliant secure messaging
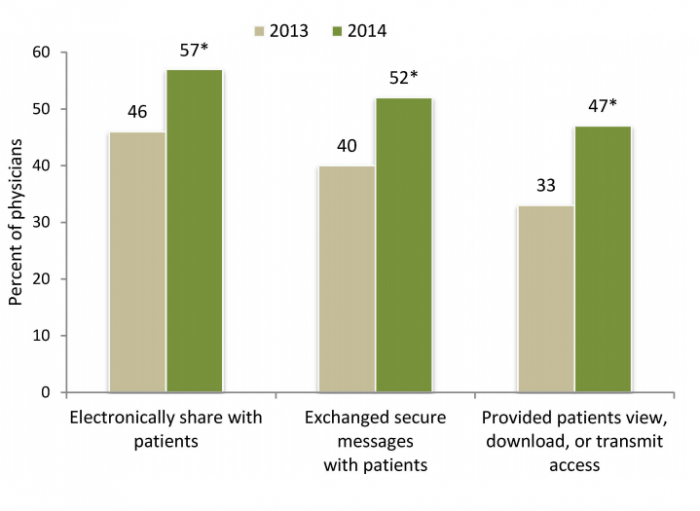
In terms of secure messaging usage, that has increased 30 percent from 2013 to 2014, according to an Office of the National Coordinator for Health Information Technology data brief. Half of surveyed physicians 52 percent said they exchanged secure messages in 2014.
Forty-two percent more physicians also said that they allowed patients the ability to view, download, or transmit access to their electronic health information.
More patients are able to take advantage of secure messaging options as well, with a separate ONC data brief showing that 51 percent of hospitals in 2014 allowed their patients to send and receive secure messages. Furthermore, 10 percent of hospitals provided secure messaging options in 2013, while 64 percent of hospitals provided it last year.
The 2015 HIMSS HIE and Direct Messaging Survey also found that many healthcare originations support Direct messaging as the method choice for exchanging data. However, there were still challenges cited about incorporating structured data into the EHR.
Secure email, helping with transitions of care, ADT notifications, patient communication, and handling consult requests between physicians were the top reported uses of Direct messaging, according to the survey.
“Use of Direct to enable HIE has been a bumpy ride and while variability exists in the market, the message should be that HIE is growing, the market is maturing and we are all learning how to better collaborate with our community partners,” HIMSS Director of Informatics Mari Greenberger and Sean Kennedy, Director, HIE, Mass eHealth Institute, wrote in a blog post at the time of the survey’s release. “The inter-organizational exchange of information in support of improved patient care is challenging, but from the feedback in this survey ‘the cost is worth the benefit.’”
Approximately half of the survey respondents also said that the cost of using Direct is worth the benefit of information exchange. Three-quarters of respondents 76 percent also reported access to a provider directory, 64 percent said they can access internal providers from that directory from within their EHR.
In terms of HIPAA compliant secure messaging, the HIPAA Security Rule does not require specific technical solutions. However, it does state that healthcare organizations must determine reasonable and appropriate safeguards.
“It is important, and therefore required by the Security Rule, for a covered entity to comply with the Technical Safeguard standards and certain implementation specifications; a covered entity may use any security measures that allow it to reasonably and appropriately do so,” the HHS HIPAA Security Series states.
For example, if a smaller provider does not utilize mobile devices, and does not have a BYOD policy in place, secure texting options might not be an applicable tool. Therefore, that provider does not need to worry about implementing mobile device management options, device encryption, or remote wipe capability.
A larger hospital on the other hand may find that those technical safeguards are necessary to ensure PHI security while physicians and staff members use mobile devices.
Date: November 28, 2016









